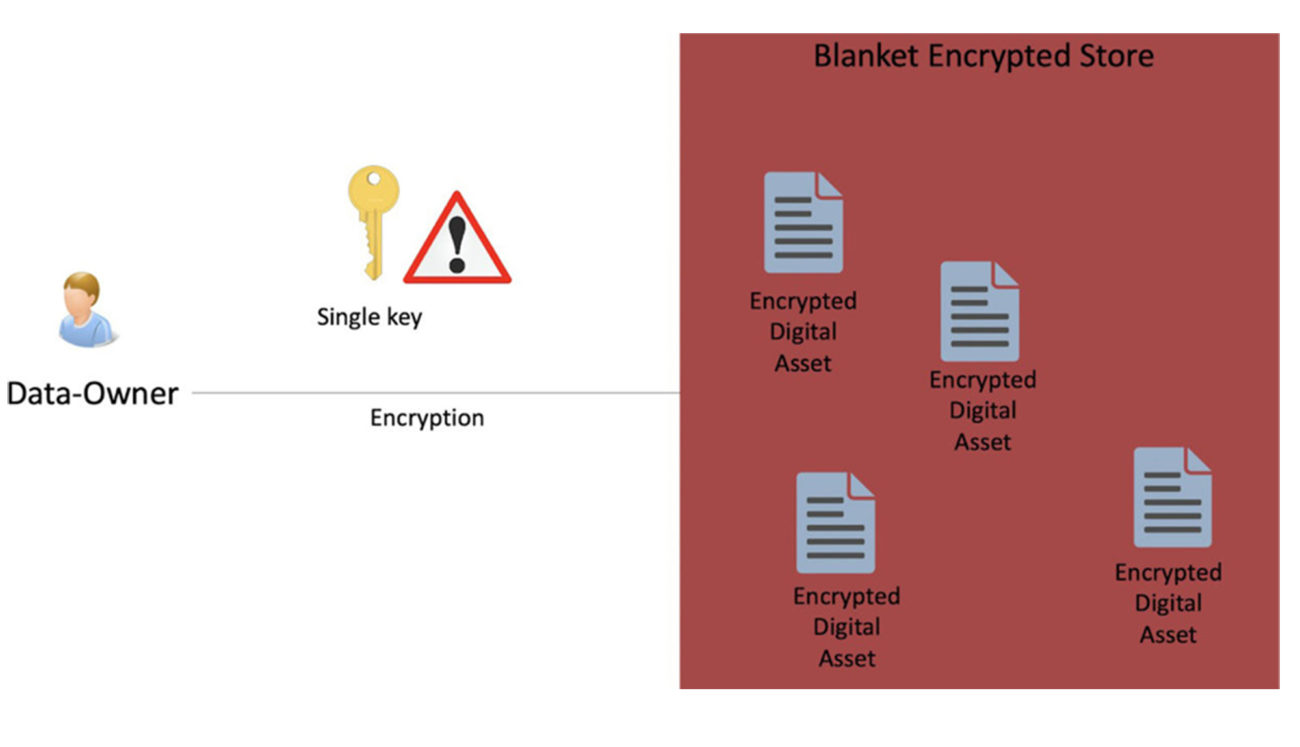
Blanket encryption with encrypted file stores or databases does not scale well in dynamic environments with frequently changing applications and machines. It also exposes all the data at once in a security breach.
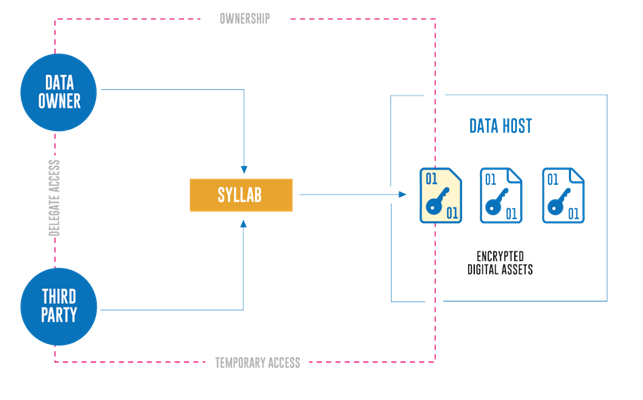
Granular encryption secures all files, objects, tokens individually. Dynamic architecture requires granular encryption where all objects are secured individually.
Encryption Features
API based encryption. Encrypt application data individually. AES 256-bit at rest as well as in transit.
High performance and scalable encryption. Ready to try the API
Full visibility of how users interact with data. Access, location, revocation provided using data visualization and searchable audit table. Compliance and security monitoring
Data moves across disperse infrastructure without a clear audit trail. Security does not scale with the growing environment. Data security is in disorder. The blanket approach does not allow encryption/decryption analysis of individual files.
Clear analytics of data usage, processing, deletion. The audit trail tracks individual data objects at all times. Granular analytics allow a full audit for compliance and security monitoring.
API Admin User
As an API admin user, you have access to your organization’s audit tab.
Location, uploads, downloads, deletion, and many other insights into how data is shared and processed.
Dashboard with audit visualization.
Ready to try the API
HIPAA, GDPR, CCPA compliance embedded in your product. Protect sensitive information and comply with privacy regulations.
Privacy compliance and security is expensive and difficult to implement. Changes in the architecture, lawyers, consultants are a significant expenditure when facing privacy regulations (HIPAA, GDPR, PDPA, CCPA).
SylLab API is offloading the burden of security and compliance to the experts for a fraction of the cost. Making consumer privacy and security a feature of your product, not a burden.
Compliance and consumer privacy embedded in your SaaS product. BAA (Business Associate Agreement) available.
Remove the burden of adopting encryption and privacy compliance.
HIPAA, GDPR, CCPA Compliance for Telemedicine Start-ups
 Non-compliance is very expensive. Organizations are stepping on thin ice when it comes to building applications that process Protected Health Information (PHI). There is a lot of overhead associated with building and implementing HIPAA-compliant systems. Understanding legal nuances and their technical implications is a mountain to climb. The risk of non-compliance with regulations is simply too high.
Non-compliance is very expensive. Organizations are stepping on thin ice when it comes to building applications that process Protected Health Information (PHI). There is a lot of overhead associated with building and implementing HIPAA-compliant systems. Understanding legal nuances and their technical implications is a mountain to climb. The risk of non-compliance with regulations is simply too high.
Copyright © 2023 SylLab Systems, Inc. All rights reserved.
| Cookie | Duration | Description |
|---|---|---|
| cookielawinfo-checkbox-analytics | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Analytics". |
| cookielawinfo-checkbox-functional | 11 months | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Functional". |
| cookielawinfo-checkbox-necessary | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Necessary". |
| cookielawinfo-checkbox-others | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Other. |
| cookielawinfo-checkbox-performance | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Performance". |
| viewed_cookie_policy | 11 months | The cookie is set by the GDPR Cookie Consent plugin and is used to store whether or not user has consented to the use of cookies. It does not store any personal data. |